
kali ni zero nak tulis tut dalam bi saja testing kalu broken maaf ye...
1) dowload ProRat.once it is download right click on the folder and choose extrack it.a pasword prompt will come up.the password will be ''pro''
2) open the progr
am.you should see the following
3) next we will create the actual trojan file .click on create and choose create proRat Server
4)next put in your ip adreess so the serv
er could not connect to you.if u don't know ur ip click on the little arror to have it filled in fo
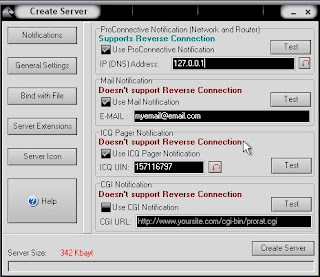
r u automaticall.next put in ur e- mail so that when and if a victem gets infected it will send u messege.we will not be using rhe rest of the option
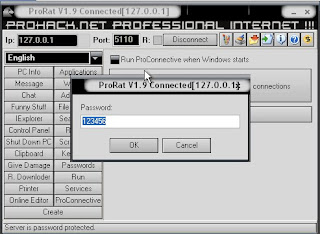
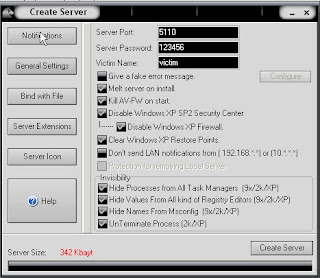
5)click on general setting button to continu
e.here we will choose the server p
ort the program will connect through,the password u will be asked to enter when victim is infected and u wish to conneconnect with them and the victem name.as u can see pro rat has the ability to disable window firewall and hide it self from being displayed in the task manager
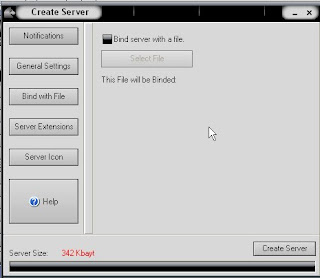
6)click on the bind with file button to continue.here u will have the option to bind trojan server file with another file remember a trojan can only be executed if a humand runs it..so by binding it with a ligimate file like a text document
or game ,the chance of some clicking it go up.check the bind option and select a file to bind it to.in the example i will use an odinarytwxt document
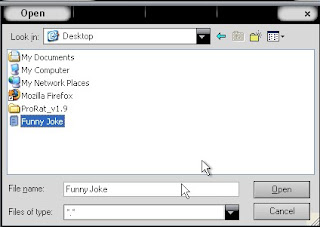
7)click on server extension button to continue.here you choose what kind of server file to generate.i willstick with the default because it has icon support,but exe's look suspicious so it would smart to change it
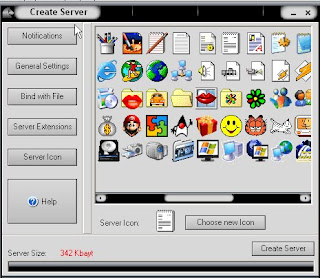
8) click on server icon to continue.here u will choose an icon for ur server file to have.the icon helps maks what the file actually is for my example i will choose reguler text document icon snincemy file is a text document
9)finally cilick on create server to,you gussed it,create server file below is what my server file looks like
10)a hacker would probably rename it to something like "funny joke'' and "game cheat" and send it as an attachment to some people.a hacker could also put it as a torent pretending it is something else ,like the latest game that just came out so he could get people to download it
11)now'i will show u what happent when victem install the server onto his computer and what hacker could do next
12)i'm going to run the server on my own computer to show u what could happen.once u run it the trojan will be install onto mycomputer in the background .the hacker would get a message telling him thaht i was infected.he would then connect my computer by typing my ip adress ,port and click connect.he will be asked for the pasword that he made when he created the server.once he type in in,he will be connected to my computer and have full control over it
13) now the hacker has a lot of option to choose from as u can see on the right .he has access to all my computer file ,he cant shut down my pc,get all my password off my computer,send a message to my computer ,formet my whole hard drive,take a screen shot and also much more
14)the image show the message i would get on my screen if the hacker choose to message me
15) bellow is an image of my task bar after the hacker click on HIDE TASKBAR BUTTON
16)bellow is an image what the hacker choose to take a screen shot of the victem screen
salam tengah malam
 Subscribe
Subscribe
2 comments:
eleh..testing konon padahal copy paste ja...:P
bapak ko aq copy paste nyampah i ingat i copy paste lagu u ke
Post a Comment